Overview
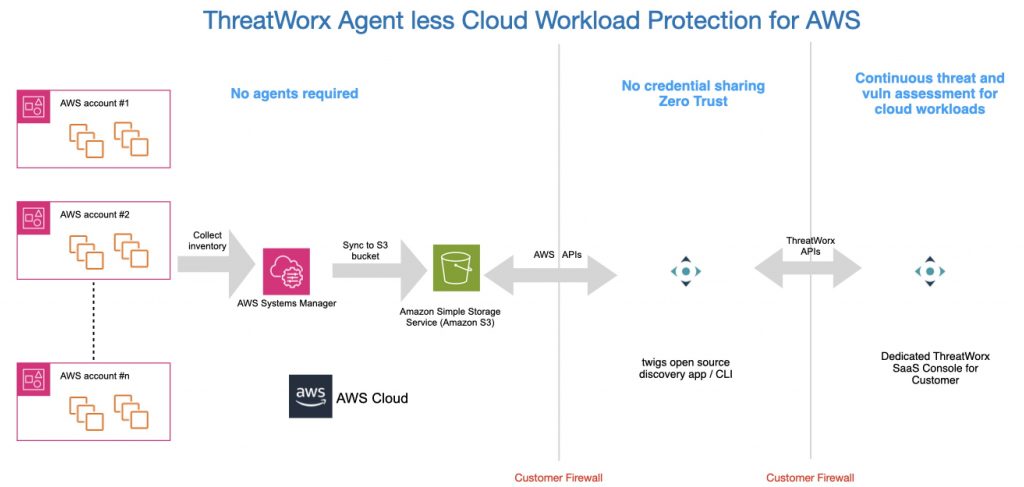
Twigs supports agent less, cloud-native discovery for AWS EC2 workloads / instances.
Pre-requisites
AWS Systems Manager needs to be configured to report asset inventory which is subsequently ingested by twigs. This is a service provided by AWS to collect and record inventory from all AWS workloads. This service needs to be enabled for the AWS subscription in order to discover the latest packages / patches and other metadata required for vulnerability assessment. For more details on how to configure AWS Systems Manager, please refer to the links below:
- AWS documentation on Systems Manager
- AWS documentation on how to inventory all managed instances in your AWS account
- ThreatWorx documentation on how to configure AWS Systems Manager
To enable AWS inventory across your organization i.e. all accounts and all regions in your organization, please follow the instructions provided here:
Setting up Systems Manager for an AWS Organization
This way you will not have to enable systems manager for inventory across individual accounts in your AWS organization.
In addition to this you can also use the cloud formation template provided by AWS to enable resource data sync to stream inventory data into one or more S3 buckets. These S3 buckets can then be used by twigs to collect inventory data. This resource data sync can also be set up manually through the AWS console for individual accounts.
Steps
After you have configured AWS Systems Manager to gather inventory, then you can run twigs to ingest this collected inventory into your ThreatWorx instance by following the below mentioned steps:
- Open a new shell / terminal
- Keep following AWS details handy to run the command:
- AWS Account Identifier (AWS_ACCOUNT)
- AWS Access Key (AWS_ACCESS_KEY)
- AWS Secret Key (AWS_SECRET_KEY)
- AWS Region (AWS_REGION)
- AWS S3 Bucket (AWS_S3_BUCKET)
- Run the command below:
twigs aws --aws_account AWS_ACCOUNT --aws_access_key AWS_ACCESS_KEY --aws_secret_key AWS_SECRET_KEY --aws_region AWS_REGION --aws_s3_bucket AWS_S3_BUCKET [--enable_tracking_tags]
- It is suggested that you enable_tracking_tags, which allows you to easily identify AWS cloud instances in ThreatWorx
- AWS cloud discovery may require some time depending on the number of EC2 instances in your AWS cloud setup.
- After discovery is complete, you can login into ThreatWorx Console to view the newly discovered assets.
Examples
$ twigs aws --aws_account "0088...324" --aws_access_key "AKIA...EQU" --aws_secret_key “Edyd...Udfbn“ --aws_region "us-west-1" --aws_s3_bucket “my_aws_inventory_s3_bucket“ --enable_tracking_tags