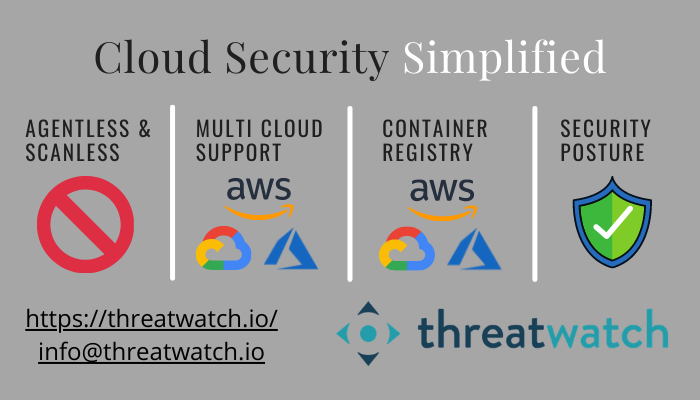
Cloud Security Simplified!
According to Gartner, pandemic-induced surge in public cloud spend is predicted to run until 2024 (reference: ComputerWeekly). This increase is fueled by organizations wanting to conserve cash, optimize IT costs and support & secure a remote workforce and ensure resiliency. Increased cloud footprint translates to an increased attack surface for most organizations. Cyber attacks on cloud […]
Cyber Insurance and Proactive Security: Not an either or proposition.

Earlier last month, CNA Financial reportedly paid a $40 million ransom after a ransomware attack and the CEO of Colonial Pipeline Co. admitted that his firm paid $4.4 million to a criminal gang after a ransomware attack led the company to shut down its 5,500 mile-long pipeline for nearly a week. It’s not clear whether Colonial Pipeline and CNA […]
Imbalance between proactive and reactive cybersecurity
NIST Cybersecurity Framework (aka Framework for Improving Critical Infrastructure Cybersecurity) is an excellent resource for all organizations. There are 3 components to the framework as below: Core – Provides a set of desired cybersecurity activities and outcomes using common language that is easy to understand. Tiers – These implementation Tiers help assist organizations by providing […]
Third Party Cyber Risk Management (TPCRM) is incomplete!
Overview In this blog article, let us take a look at the current approach to Third Party Cyber Risk Management (TPCRM), what it leaves on the table and what is really desirable. Most organizations today work closely with their business ecosystem which is key for business continuity. This business ecosystem includes but is not limited […]
Proactive Security of your AWS Cloud
Cloud adoption has increased exponentially over the years. 94% of enterprises use the cloud already. There used to be two main camps of cloud users as below: Cloud users who were skeptical of security of public cloud in the first place. Cloud users who believe that public cloud takes care of all security aspects automatically […]
Gartner Top Security Projects for 2020-21
Security and risk folks are constantly trying to improve security without impacting business productivity. It is key to determine which projects will drive most business value while reducing risk. In September 2020, Gartner published their recommendations for Top 10 Security Projects for 2020-21 that security and risk management leaders should focus on. Here is a […]
Frictionless Vulnerability Assessment
Vulnerability assessment and management is a critical piece in the cybersecurity program for any organization. Most organizations perform periodic vulnerability scans. However, traditional vulnerability scanning tools have largely resulted in a painful experience for customers. This is due to multiple reasons as below: Need to install agents or scanner appliances across the fleet These agents […]
Don’t stop at “VA” for your cloud, but assess complete security posture.
Organizations have increased public cloud usage, as there are obvious benefits (elasticity, pay-as-you-go subscription model, etc.). While adoption across cloud layers (IaaS, PaaS, SaaS) varies across organizations, one thing for sure is that IaaS usage is most prevalent. Organizations end up shifting to the cloud in an urgency and likely with a “lift and shift” […]
Vulnerability management for your remote workforce using ThreatWorx
In an earlier blog article, we had a look at the challenges that organizations are facing with vulnerability management (VM) for their remote workforce. We briefly described what a Next Generation Vulnerability Management solution should look like for these scenarios. To summarize a Next Generation VM needs to be a cloud-based service which can provide […]
Vulnerability management for remote workforce
Businesses always have had some remote workforce, but the current pandemic has resulted in an increased remote workforce. For most organizations nearly 90-100% workforce is now operating remotely (mostly work from home [WFH] cases). Functioning of this remote workforce is critical for business continuity. This has resulted in many sudden adjustments for IT and Security […]
